KringleCon3 2020 Objective Three Writeup: Point-of-Sale Password Recovery
KringleCon3 Overview
KringleCon is the annual Holiday Hacking Challenge put on by the SANS Institute. Players are presented with a variety of security themed objectives and CLI challenges which provide valuable hints. In addition, the KringleCon YouTube Channel provides additional training, helpful for solving obstacles within the game, as well as practical security advice outside the game.
When KringleCon is over, players publish writeups. Each player tackles the objectives in their own unique way. These writeups help us gain insight into the minds of each individual player.
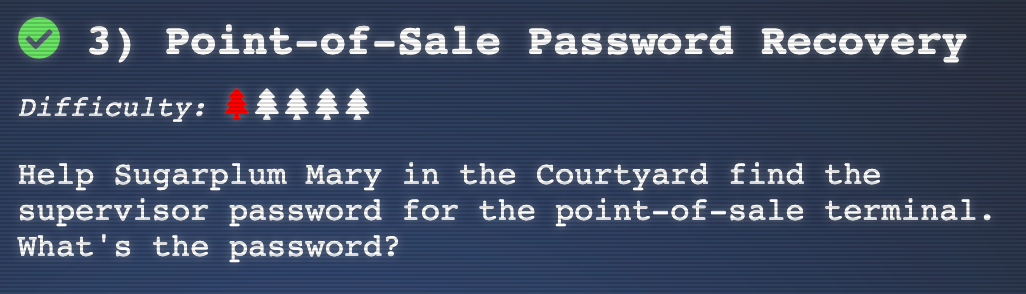
Objective Overview
Help Sugarplum Mary in the Courtyard find the supervisor password for the point-of-sale terminal. What’s the password?
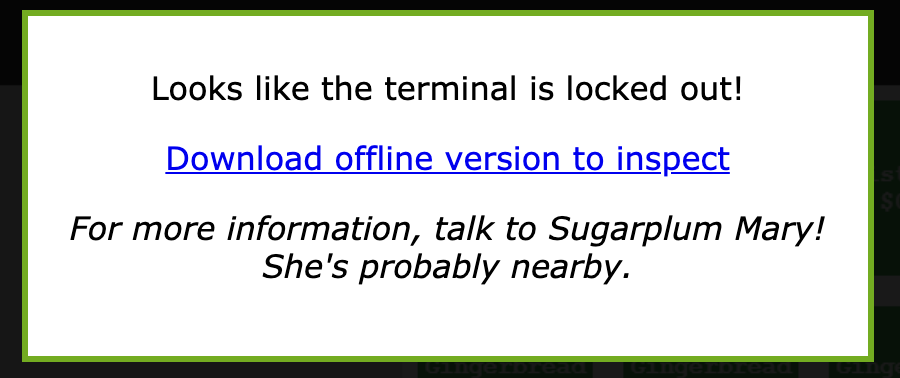
We need to download a file to complete this challenge:
Elf Hints
Shinny says this might be an Electron application.
I hear there’s a way to extract an ASAR file from the binary, but I haven’t looked into it yet.
Objective Detailed Writeup
Initial Findings
I copied the file to a Linux server for inspection:
jemurray@shell:~/santa-shop$ file santa-shop.exe
santa-shop.exe: PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive
Assumptions After Initial Observations
- The file is a self-extracting archive, there must be more files within the
.exeto examine - Based on the hint this is an electron application and ASAR file
- The password is probably in clear text somewhere
- May have to use
stringsto look though binary files unzipwill open the file
Solving
Tried unsuccessfully to use unzip to decompress the file:
jemurray@shell:~/santa-shop$ unzip santa-shop.exe
Archive: santa-shop.exe
End-of-central-directory signature not found. Either this file is not
a zipfile, or it constitutes one disk of a multi-part archive. In the
latter case the central directory and zipfile comment will be found on
the last disk(s) of this archive.
unzip: cannot find zipfile directory in one of santa-shop.exe or
santa-shop.exe.zip, and cannot find santa-shop.exe.ZIP, period.
After a few Google searches, Nullsoft Installer self-extracting archive are 7-Zip archives. This software is not install on Ubuntu by default. Install with:
sudo apt install p7zip-full
Extracting the file with 7z:
jemurray@shell:~$ 7z e santa-shop.exe
7-Zip [64] 16.02 : Copyright (c) 1999-2016 Igor Pavlov : 2016-05-21
p7zip Version 16.02 (locale=en_US.UTF-8,Utf16=on,HugeFiles=on,64 bits,1 CPU Intel(R) Xeon(R) Gold 6248 CPU @ 2.50GHz (50657),ASM,AES-NI)
Scanning the drive for archives:
1 file, 49824644 bytes (48 MiB)
## Extracting archive: santa-shop.exe
Path = santa-shop.exe
Type = Nsis
Physical Size = 49824644
Method = Deflate
Solid = -
Headers Size = 102546
Embedded Stub Size = 57856
SubType = NSIS-3 Unicode BadCmd=11
Everything is Ok
Files: 9
Size: 50033887
Compressed: 49824644
That worked, there are more files to investigate:
jemurray@shell:~/santa-shop$ ls -al
total 97544
drwxr-xr-x 3 jemurray jemurray 4096 Dec 20 19:51 .
drwxr-xr-x 27 jemurray jemurray 4096 Dec 13 13:37 ..
-rw-r--r-- 1 jemurray jemurray 49323645 Dec 4 17:47 app-64.7z
-rw-r--r-- 1 jemurray jemurray 6656 Dec 13 13:22 nsExec.dll
-rw-r--r-- 1 jemurray jemurray 434176 Dec 13 13:22 nsis7z.dll
-rw-r--r-- 1 jemurray jemurray 4608 Dec 13 13:22 nsProcess.dll
-rw-r--r-- 1 jemurray jemurray 49824644 Dec 13 13:22 santa-shop.zip
-rw-r--r-- 1 jemurray jemurray 9216 Dec 13 13:22 SpiderBanner.dll
-rw-r--r-- 1 jemurray jemurray 102400 Dec 13 13:22 StdUtils.dll
-rw-r--r-- 1 jemurray jemurray 12288 Dec 13 13:22 System.dll
-rw-r--r-- 1 jemurray jemurray 137826 Dec 4 17:47 'Uninstall santa-shop.exe'
-rw-r--r-- 1 jemurray jemurray 3072 Dec 13 13:22 WinShell.dll
Inside this archive is another 7z file to extract. Based on the name of the file app-64.7z this is probably the application we need to evaluate:
# Create a directory first
mkdir app
# Copy the file to this new directory
cp app-64.7z app
# Enter the dir
cd app
# Uncompress the files
7z e app-64.7z app
One of the hints talked about asar files. There is one in the newly extracted directory:
jemurray@shell:~/santa-shop/app$ ls -al *asar*
-rw-r--r-- 1 jemurray jemurray 136143 Dec 13 13:38 app.asar
What type of file is this:
jemurray@shell:~/santa-shop/app$ file app.asar
app.asar: data
Does it have any strings that look like a password? It does:
jemurray@shell:~/santa-shop/app$ grep -i pass app.asar
Binary file app.asar matches
Use strings to look into binary files. Found the password:
jemurray@shell:~/santa-shop/app$ strings app.asar | grep -i pass
Remember, if you need to change Santa's passwords, it's at the top of main.js!
const SANTA_PASSWORD = 'santapass';
Answer
The password is: santapass